A better user secrets tool
Storing secret values such as API keys, connection strings etc with your code is something that should be avoided. If you have an ASP.NET Core project you get a useful tool for this with the Secret Manager Tool.
With this tool, you can quite easily add and remove secrets from your project by using CLI commands as seen below.
1
2
3
> dotnet user-secrets set "MyApiKey" "apikey-123"
> dotnet user-secrets list
This works great, but it isn’t really that intuitive and if you list a lot of secrets it can easily get messy to read.
1
2
3
4
5
6
7
8
> dotnet user-secrets list
MySecretKey = d7f99c2b-b989-4579-b51d-2b22b89d0aaa
MySecret = Boo
keyvaultsecret = This is a key vault secret
keyvault:nestedsecret = nested key vault sescret
ConnectionString = Server=myServer;Database=myDB;User Id=myUser;Password=myPass;
ApiKey = 12345-ABCDE-67890-FGHIJ-KLMNO-PQRST-UVWXYZ-98765-43210-ZYXWV-UTSRQ-PONML-KJIHG-FEDCBA-54321-ABCDE-12345-FGHIJ-KLMNO-PQRST-UVWXYZ
AnotherSecret = SomeSecretValue
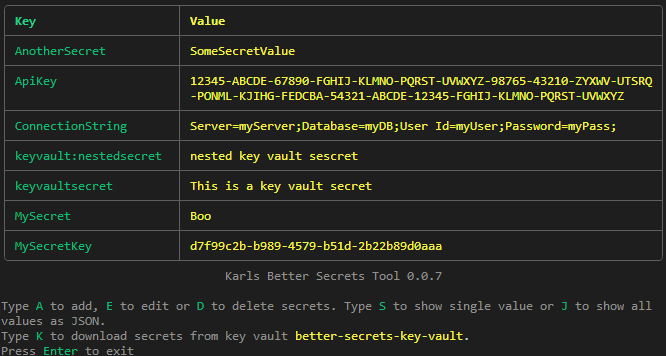
To get around this (and to make it easier for some of my less CLI inclined colleagues) I set out to create a better tool to manage user secrets.
There are few things I want to improve with this tool.
- A better list of secrets
- Make it easier to manage (add, edit, remove) secrets for those who don’t want to remember the exact CLI arguments.
- I want to be able to run the tool in more places in my solution, not just in the ASP.NET Core project folder.
I also wanted to incorporate something I use in a few projects where I sync secrets from an azure keyvault. This has been a powershell script which works fine, but it requires everyone to install powershell to get started which isn’t optimal.
Introducing “Karls Better Secrets Tool”
After a few evenings of coding (and looking through the ASP.NET Core sources to figure out how the regular tool works) I ended up with my new .NET Tool Karls Better Secrets Tool.
If you are on .NET 10 you can easily test it out in your project via the dnx script (in your project folder).
1
> dnx Karls.BetterSecretsTool
Then when you realize how awesome it is you can add it to your project as a .NET Tool so it can be easily restored for your colleagues.
1
2
> dotnet new tool-manifest # if you don't have a manifest already
> dotnet tool install Karls.BetterSecretsTool
Downloading secrets from an Azure Key Vault
As I mentioned above I have a setup that downloads secrets from an Azure Key Vault.
I’ve seen way to many projects where the secrets are shared by emailing the JSON file with the secrets or people spending way to much time entering 10+ secrets via the CLI (still shared via Slack or email) and then failing by not adding quotations around the values.
Since we use key vaults to store the secrets for our deployed services it felt like a no-brainer to use a key vault to share out local secrets as well. We could use the secrets directly from the key vault, but that will require the key vault to be accessible to start the project which isn’t always feasible.
To set this up with the tool you need to add the key vault name to your .csproj (or Directory.Build.props) like this.
1
2
3
4
<PropertyGroup>
<UserSecretsId>f626a917-9d68-4eb6-8742-f2032d8f602c</UserSecretsId>
<UserSecretsKeyVault>my-project-local-keyvault</UserSecretsKeyVault>
</PropertyGroup>
Any users who should be able to download secrets also need the Key Vault Secrets User RBAC role assigned. When the key vault name is found by the tool, it shows the option to download secrets.